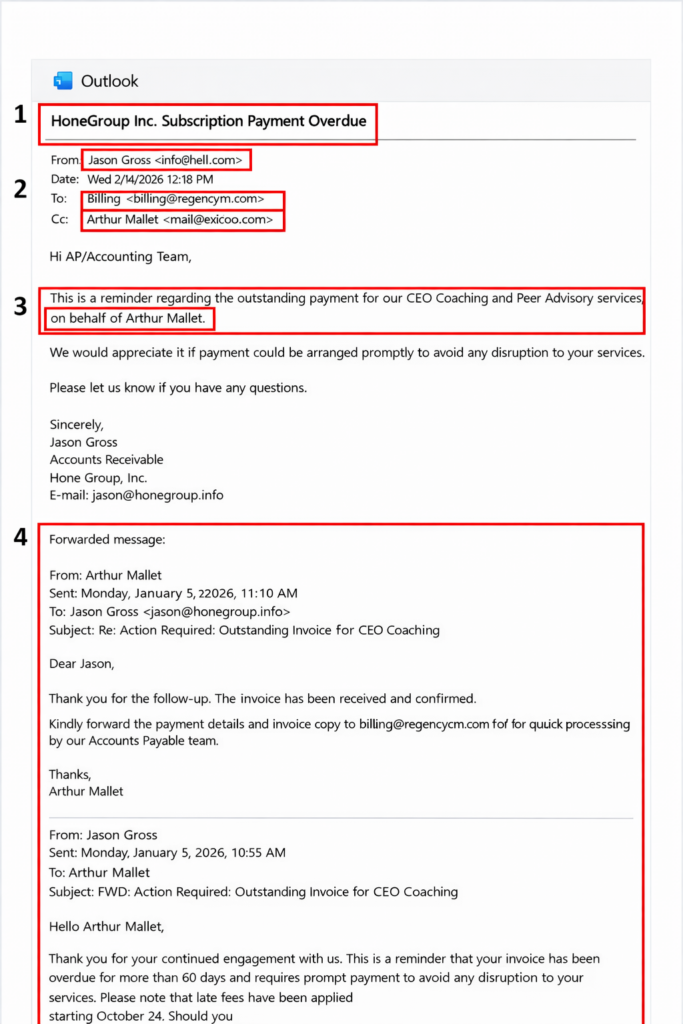
Last month I received an email (pictured below for your enjoyment and reference) that inspired me to write about this topic which is becoming one of the most annoying side effects of technological advancement. It’s not a new tactic, but with AI the frequency and sophistication have seemingly been ramped up to new highs.
Cybercriminals are increasingly targeting individuals through phishing emails – messages designed to trick recipients into revealing sensitive information or taking harmful actions.
These emails often appear convincing. They may reference familiar names, imitate legitimate companies, or create pressure to act quickly.
The good news is that most phishing attempts rely on predictable tactics. By recognizing these patterns, you can significantly reduce the risk of falling victim to a scam.
Below are four common warning signs to watch for (all were included in the recent attempt targeting Regency Capital).
1. A False Sense of Urgency
One of the most common tactics used in phishing scams is manufactured urgency.
The message may claim that:
- An account requires immediate verification
- A payment must be approved quickly
- A security issue requires urgent action
The goal is to encourage a response before the recipient has time to verify the request.
Legitimate financial institutions rarely demand immediate action through unexpected email requests. If a message pressures you to act right away, it’s best to pause and confirm its authenticity.
2. Email Spoofing
Another common tactic is email spoofing.
Email spoofing occurs when a cybercriminal disguises the sender’s address so the email appears to come from a trusted source. The sender name may look familiar, but the actual email address behind it is slightly different.
For example, an email might appear to come from a legitimate organization but originate from a domain that is only subtly altered.
Always check the full sender address, not just the name displayed in your inbox.
3. Referencing Someone in Authority
Phishing emails often reference senior executives or management-level individuals.
Attackers know that people are more likely to respond quickly when they believe a request comes from someone in authority.
These messages may include requests to:
- Share confidential information
- Approve payments or transfers
- Provide login credentials
If an email references someone in a leadership role but the request seems unusual, it is wise to verify the request directly through another communication channel.
4. Fabricated Message History
Some phishing emails include fake message threads designed to make the email appear legitimate.
Attackers may insert a fabricated conversation into the email body so it looks like the request is part of an ongoing discussion.
This tactic increases credibility because recipients may assume the communication has already been verified.
If you receive a message that appears to be part of a conversation you were not previously involved in, take a moment to confirm before responding.
A Simple Rule for Suspicious Emails
If an email asks you to:
- Share sensitive information
- Click a link to access an account
- Download an unexpected attachment
- Transfer money or authorize a transaction
pause and verify the request first.
The safest approach is to contact the sender directly using a known phone number or trusted contact method. We pride ourselves on having a person answer the phone and we genuinely enjoy speaking to all of our clients so never hesitate to give us a call.
Our Commitment to Cybersecurity
Protecting client information is a top priority. We maintains multiple safeguards designed to protect sensitive data and monitor potential threats.
However, cybersecurity is most effective when technology and awareness work together.
If you ever receive a message that appears to involve Regency Capital or any of your financial institutions but seems unusual, please contact us directly before taking action.



